Ecosystm research shows that cybersecurity is the most discussed technology at the Board and Management level, driven by the increasing sophistication of cyber threats and the rapid adoption of AI. While AI enhances security, it also introduces new vulnerabilities. As organisations face an evolving threat landscape, they are adopting a more holistic approach to cybersecurity, covering prevention, detection, response, and recovery.
In 2025, cybersecurity leaders will continue to navigate a complex mix of technological advancements, regulatory pressures, and changing business needs. To stay ahead, organisations will prioritise robust security solutions, skilled professionals, and strategic partnerships.
Ecosystm analysts Darian Bird, Sash Mukherjee, and Simona Dimovski present the key cybersecurity trends for 2025.
Click here to download ‘Securing the AI Frontier: Top 5 Cyber Trends for 2025’ as a PDF
1. Cybersecurity Will Be a Critical Differentiator in Corporate Strategy
The convergence of geopolitical instability, cyber weaponisation, and an interconnected digital economy will make cybersecurity a cornerstone of corporate strategy. State-sponsored cyberattacks targeting critical infrastructure, supply chains, and sensitive data have turned cyber warfare into an operational reality, forcing businesses to prioritise security.
Regulatory pressures are driving this shift, mandating breach reporting, data sovereignty, and significant penalties, while international cybersecurity norms compel companies to align with evolving standards to remain competitive.
The stakes are high. Stakeholders now see cybersecurity as a proxy for trust and resilience, scrutinising both internal measures and ecosystem vulnerabilities.

2. Zero Trust Architectures Will Anchor AI-Driven Environments
The future of cybersecurity lies in never trusting, always verifying – especially where AI is involved.
In 2025, the rise of AI-driven systems will make Zero Trust architectures vital for cybersecurity. Unlike traditional networks with implicit trust, AI environments demand stricter scrutiny due to their reliance on sensitive data, autonomous decisions, and interconnected systems. The growing threat of adversarial attacks – data poisoning, model inversion, and algorithmic manipulation – highlights the urgency of continuous verification.
Global forces are driving this shift. Regulatory mandates like the EU’s DORA, the US Cybersecurity Executive Order, and the NIST Zero Trust framework call for robust safeguards for critical systems. These measures align with the growing reliance on AI in high-stakes sectors like Finance, Healthcare, and National Security.

3. Organisations Will Proactively Focus on AI Governance & Data Privacy
Organisations are caught between excitement and uncertainty regarding AI. While the benefits are immense, businesses struggle with the complexities of governing AI. The EU AI Act looms large, pushing global organisations to brace for stricter regulations, while a rise in shadow IT sees business units bypassing traditional IT to deploy AI independently.
In this environment of regulatory ambiguity and organisational flux, CISOs and CIOs will prioritise data privacy and governance, proactively securing organisations with strong data frameworks and advanced security solutions to stay ahead of emerging regulations.
Recognising that AI will be multi-modal, multi-vendor, and hybrid, organisations will invest in model orchestration and integration platforms to simplify management and ensure smoother compliance.

4. Network & Security Stacks Will Streamline Through Converged Platforms
This shift stems from the need for unified management, cost efficiency, and the recognition that standardisation enhances security posture.
Tech providers are racing to deliver comprehensive network and security platforms.
Recent M&A moves by HPE (Juniper), Palo Alto Networks (QRadar SaaS), Fortinet (Lacework), and LogRhythm (Exabeam) highlight this trend. Rising player Cato Networks is capitalising on mid-market demand for single-provider solutions, with many customers planning to consolidate vendors in their favour. Meanwhile, telecoms are expanding their SASE offerings to support organisations adapting to remote work and growing cloud adoption.

5. AI Will Be Widely Used to Combat AI-Powered Threats in Real-time
By 2025, the rise of AI-powered cyber threats will demand equally advanced AI-driven defences.
Threat actors are using AI to launch adaptive attacks like deepfake fraud, automated phishing, and adversarial machine learning, operating at a speed and scale beyond traditional defences.
Real-time AI solutions will be essential for detection and response.
Nation-state-backed advanced persistent threat (APT) groups and GenAI misuse are intensifying these challenges, exploiting vulnerabilities in critical infrastructure and supply chains. Mandatory reporting and threat intelligence sharing will strengthen AI defences, enabling real-time adaptation to emerging threats.
Despite financial institutions’ unwavering efforts to safeguard their customers, scammers continually evolve to exploit advancements in technology. For example, the number of scams and cybercrimes reported to the police in Singapore increased by a staggering 49.6% to 50,376 at an estimated cost of USD 482M in 2023. GenAI represents the latest challenge to the industry, providing fraudsters with new avenues for deception.
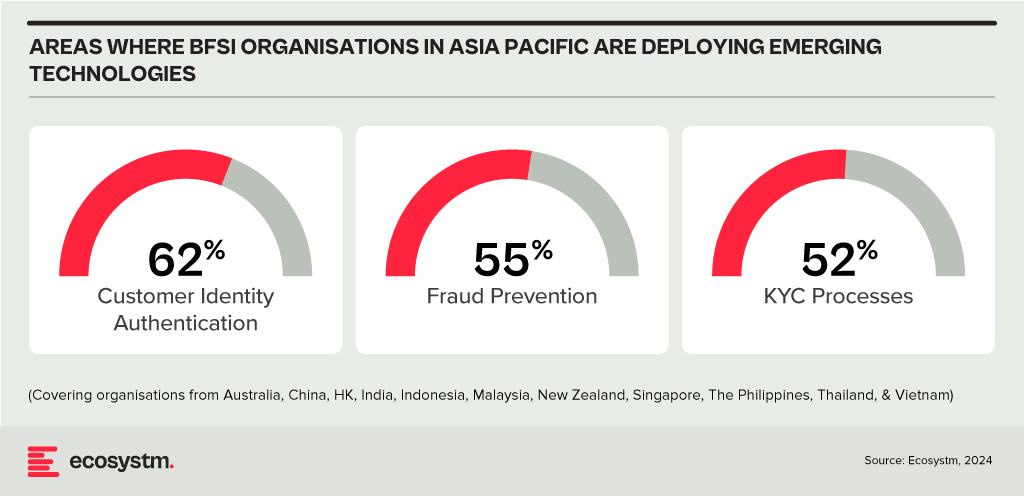
Ecosystm research shows that BFSI organisations in Asia Pacific are spending more on technologies to authenticate customer identity and prevent fraud, than they are in their Know Your Customer (KYC) processes.
The Evolution of the Threat Landscape in BFSI
Synthetic Identity Fraud. This involves the creation of fictitious identities by combining real and fake information, distinct from traditional identity theft where personal data is stolen. These synthetic identities are then exploited to open fraudulent accounts, obtain credit, or engage in financial crimes, often evading detection due to their lack of association with real individuals. The Deloitte Centre for Financial Services predicts that synthetic identity fraud will result in USD 23B in losses by 2030. Synthetic fraud is posing significant challenges for financial institutions and law enforcement agencies, especially with the emergence of advanced technologies like GenAI being used to produce realistic documents blending genuine and false information, undermining Know Your Customer (KYC) protocols.
AI-Enhanced Phishing. Ecosystm research reveals that in Asia Pacific, 71% of customer interactions in BFSI occur across multiple digital channels, including mobile apps, emails, messaging, web chats, and conversational AI. In fact, 57% of organisations plan to further improve customer self-service capabilities to meet the demand for flexible and convenient service delivery. The proliferation of digital channels brings with it an increased risk of phishing attacks.
While these organisations continue to educate their customers on how to secure their accounts in a digital world, GenAI poses an escalating threat here as well. Phishing schemes will employ widely available LLMs to generate convincing text and even images. For many potential victims, misspellings and strangely worded appeals are the only hint that an email from their bank is not what it seems. The maturing of deepfake technology will also make it possible for malicious agents to create personalised voice and video attacks.
Identity Fraud Detection and Prevention
Although fraudsters are exploiting every new vulnerability, financial organisations also have new tools to protect their customers. Organisations should build a layered defence to prevent increasingly sophisticated attempts at fraud.
- Behavioural analytics. Using machine learning, financial organisations can differentiate between standard activities and suspicious behaviour at the account level. Data that can be analysed includes purchase patterns, unusual transaction values, VPN use, browser choice, log-in times, and impossible travel. Anomalies can be flagged, and additional security measures initiated to stem the attack.
- Passive authentication. Accounts can be protected even before password or biometric authentication by analysing additional data, such as phone number and IP address. This approach can be enhanced by comparing databases populated with the details of suspicious actors.
- SIM swap detection. SMS-based MFA is vulnerable to SIM swap attacks where a customer’s phone number is transferred to the fraudster’s own device. This can be prevented by using an authenticator app rather than SMS. Alternatively, SIM swap history can be detected before sending one-time passwords (OTPs).
- Breached password detection. Although customers are strongly discouraged to reuse passwords across sites, some inevitably will. By employing a service that maintains a database of credentials leaked during third-party breaches, it is possible to compare with active customer passwords and initiate a reset.
- Stronger biometrics. Phone-based fingerprint recognition has helped financial organisations safeguard against fraud and simplify the authentication experience. Advances in biometrics continue with recognition for faces, retina, iris, palm print, and voice making multimodal biometric protection possible. Liveness detection will grow in importance to combat against AI-generated content.
- Step-up validation. Authentication requirements can be differentiated according to risk level. Lower risk activities, such as balance check or internal transfer, may only require minimal authentication while higher risk ones, like international or cryptocurrency transactions may require a step up in validation. When anomalous behaviour is detected, even greater levels of security can be initiated.
Recommendations
- Reduce friction. While it may be tempting to implement heavy handed approaches to prevent fraud, it is also important to minimise friction in the authentication system. Frustrated users may abandon services or find risky ways to circumvent security. An effective layered defence should act in the background to prevent attackers getting close.
- AI Phishing Awareness. Even the savviest of customers could fall prey to advanced phishing attacks that are using GenAI. Social engineering at scale becomes increasingly more possible with each advance in AI. Monitor emerging global phishing activities and remind customers to be ever vigilant of more polished and personalised phishing attempts.
- Deploy an authenticator app. Consider shifting away from OTP SMS as an MFA method and implement either an authenticator app or one embedded in the financial app instead.
- Integrate authentication with fraud analytics. Select an authentication provider that can integrate its offering with analytics to identify fraud or unusual behaviour during account creation, log in, and transactions. The two systems should work in tandem.
- Take a zero-trust approach. Protecting both customers and employees is critical, particularly in the hybrid work era. Implement zero trust tools to prevent employees from falling victim to malicious attacks and minimising damage if they do.

In the Ecosystm Predicts: Building an Agile & Resilient Organisation: Top 5 Trends in 2024, Principal Advisor Darian Bird said, “The emergence of Generative AI combined with the maturing of deepfake technology will make it possible for malicious agents to create personalised voice and video attacks.” Darian highlighted that this democratisation of phishing, facilitated by professional-sounding prose in various languages and tones, poses a significant threat to potential victims who rely on misspellings or oddly worded appeals to detect fraud. As we see more of these attacks and social engineering attempts, it is important to improve defence mechanisms and increase awareness.
Understanding Deepfake Technology
The term Deepfake is a combination of the words ‘deep learning’ and ‘fake’. Deepfakes are AI-generated media, typically in the form of images, videos, or audio recordings. These synthetic content pieces are designed to appear genuine, often leading to the manipulation of faces and voices in a highly realistic manner. Deepfake technology has gained spotlight due to its potential for creating convincing yet fraudulent content that blurs the line of reality.
Deepfake algorithms are powered by Generative Adversarial Networks (GANs) and continuously enhance synthetic content to closely resemble real data. Through iterative training on extensive datasets, these algorithms refine features such as facial expressions and voice inflections, ensuring a seamless emulation of authentic characteristics.
Deepfakes Becoming Increasingly Convincing
Hyper-realistic deepfakes, undetectable to the human eye and ear, have become a huge threat to the financial and technology sectors. Deepfake technology has become highly convincing, blurring the line between real and fake content. One of the early examples of a successful deepfake fraud was when a UK-based energy company lost USD 243k through a deepfake audio scam in 2019, where scammers mimicked the voice of their CEO to authorise an illegal fund transfer.
Deepfakes have evolved from audio simulations to highly convincing video manipulations where faces and expressions are altered in real-time, making it hard to distinguish between real and fake content. In 2022, for instance, a deepfake video of Elon Musk was used in a crypto scam that resulted in a loss of about USD 2 million for US consumers. This year, a multinational company in Hong Kong lost over USD 25 million when an employee was tricked into sending money to fraudulent accounts after a deepfake video call by what appeared to be his colleagues.
Regulatory Responses to Deepfakes
Countries worldwide are responding to the challenges posed by deepfake technology through regulations and awareness campaigns.
- Singapore’s Online Criminal Harms Act, that will come into effect in 2024, will empower authorities to order individuals and Internet service providers to remove or block criminal content, including deepfakes used for malicious purposes.
- The UAE National Programme for Artificial Intelligence released a deepfake guide to educate the public about both harmful and beneficial applications of this technology. The guide categorises fake content into shallow and deep fakes, providing methods to detect deepfakes using AI-based tools, with a focus on promoting positive uses of advanced technologies.
- The proposed EU AI Act aims to regulate them by imposing transparency requirements on creators, mandating them to disclose when content has been artificially generated or manipulated.
- South Korea passed a law in 2020 banning the distribution of harmful deepfakes. Offenders could be sentenced to up to five years in prison or fined up to USD 43k.
- In the US, states like California and Virginia have passed laws against deepfake pornography, while federal bills like the DEEP FAKES Accountability Act aim to mandate disclosure and counter malicious use, highlighting the diverse global efforts to address the multifaceted challenges of deepfake regulation.
Detecting and Protecting Against Deepfakes
Detecting deepfake becomes increasingly challenging as technology advances. Several methods are needed – sometimes in conjunction – to be able to detect a convincing deepfake. These include visual inspection that focuses on anomalies, metadata analysis to examine clues about authenticity, forensic analysis for pattern and audio examination, and machine learning that uses algorithms trained on real and fake video datasets to classify new videos.
However, identifying deepfakes requires sophisticated technology that many organisations may not have access to. This heightens the need for robust cybersecurity measures. Deepfakes have seen an increase in convincing and successful phishing – and spear phishing – attacks and cyber leaders need to double down on cyber practices.
Defences can no longer depend on spotting these attacks. It requires a multi-pronged approach which combines cyber technologies, incidence response, and user education.
Preventing access to users. By employing anti-spoofing measures organisations can safeguard their email addresses from exploitation by fraudulent actors. Simultaneously, minimising access to readily available information, particularly on websites and social media, reduces the chance of spear-phishing attempts. This includes educating employees about the implications of sharing personal information and clear digital footprint policies. Implementing email filtering mechanisms, whether at the server or device level, helps intercept suspicious emails; and the filtering rules need to be constantly evaluated using techniques such as IP filtering and attachment analysis.
Employee awareness and reporting. There are many ways that organisations can increase awareness in employees starting from regular training sessions to attack simulations. The usefulness of these sessions is often questioned as sometimes they are merely aimed at ticking off a compliance box. Security leaders should aim to make it easier for employees to recognise these attacks by familiarising them with standard processes and implementing verification measures for important email requests. This should be strengthened by a culture of reporting without any individual blame.
Securing against malware. Malware is often distributed through these attacks, making it crucial to ensure devices are well-configured and equipped with effective endpoint defences to prevent malware installation, even if users inadvertently click on suspicious links. Specific defences may include disabling macros and limiting administrator privileges to prevent accidental malware installation. Strengthening authentication and authorisation processes is also important, with measures such as multi-factor authentication, password managers, and alternative authentication methods like biometrics or smart cards. Zero trust and least privilege policies help protect organisation data and assets.
Detection and Response. A robust security logging system is crucial, either through off-the shelf monitoring tools, managed services, or dedicated teams for monitoring. What is more important is that the monitoring capabilities are regularly updated. Additionally, having a well-defined incident response can swiftly mitigate post-incident harm post-incident. This requires clear procedures for various incident types and designated personnel for executing them, such as initiating password resets or removing malware. Organisations should ensure that users are informed about reporting procedures, considering potential communication challenges in the event of device compromise.
Conclusion
The rise of deepfakes has brought forward the need for a collaborative approach. Policymakers, technology companies, and the public must work together to address the challenges posed by deepfakes. This collaboration is crucial for making better detection technologies, establishing stronger laws, and raising awareness on media literacy.

Ecosystm research reveals a stark reality: 75% of technology leaders in Financial Services anticipate data breaches.
Given the sector’s regulatory environment, data breaches carry substantial financial implications, emphasising the critical importance of giving precedence to cybersecurity. This is compelling a fresh cyber strategy focused on early threat detection and reduction of attack impact.
Read on to find out how tech leaders are building a culture of cyber-resilience, re-evaluating their cyber policies, and adopting technologies that keep them one step ahead of their adversaries.
Download ‘Cyber-Resilience in Finance: People, Policy & Technology’ as a PDF
The Banking, Financial Services, and Insurance (BFSI) industry, known for its cautious stance on technology, is swiftly undergoing a transformational modernisation journey. Areas such as digital customer experiences, automated fraud detection, and real-time risk assessment are all part of a technology-led roadmap. This shift is transforming the cybersecurity stance of BFSI organisations, which have conventionally favoured centralising everything within a data centre behind a firewall.
Ecosystm research finds that 75% of BFSI technology leaders believe that a data breach is inevitable. This requires taking a new cyber approach to detect threats early, reduce the impact of an attack, and avoid lateral movement across the network.
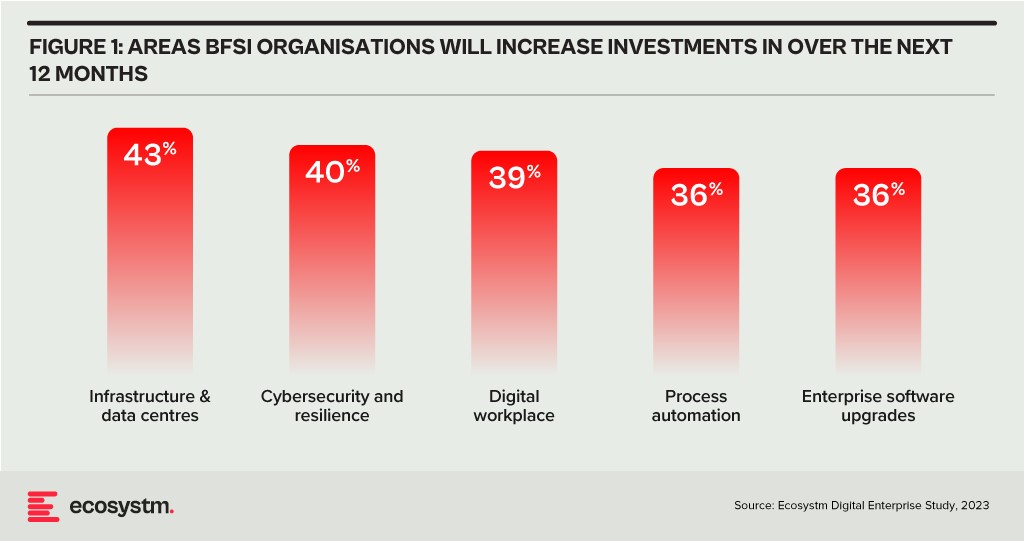
BFSI organisations will boost investments in two main areas over the next year: updating infrastructure and software, and exploring innovative domains like digital workplaces and automation. Cybersecurity investments are crucial in both of these areas.
As a regulated industry, breaches come with significant cost implications, underscoring the need to prioritise cybersecurity. BFSI cybersecurity and risk teams need to constantly reassess their strategies for safeguarding data and fulfilling compliance obligations, as they explore ways to facilitate new services for customers, partners, and employees.
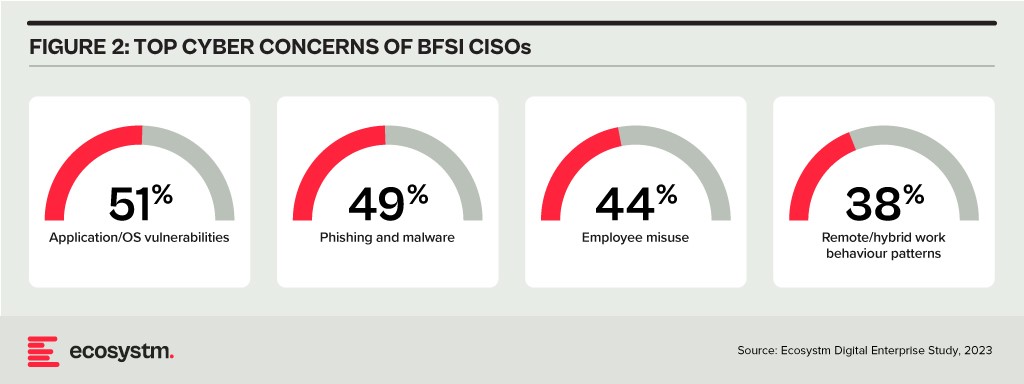
The primary concerns of BFSI CISOs can be categorised into two distinct groups:
- Expanding Technology Use. This includes the proliferation of applications and devices, as well as data access beyond the network perimeter.
- Employee-Related Vulnerabilities. This involves responses to phishing and malware attempts, as well as intentional and unintentional misuse of technology.
Vulnerabilities Arising from Employee Actions
Security vulnerabilities arising from employee actions and unawareness represent a significant and ongoing concern for businesses of all sizes and industries – the risks are just much bigger for BFSI. These vulnerabilities can lead to data breaches, financial losses, damage to reputation, and legal ramifications. A multi-pronged approach is needed that combines technology, training, policies, and a culture of security consciousness.
Training and Culture. BFSI organisations prioritise comprehensive training and awareness programs, educating employees about common threats like phishing and best practices for safeguarding sensitive data. While these programs are often ongoing and adaptable to new threats, they can sometimes become mere compliance checklists, raising questions about their true effectiveness. Conducting simulated phishing attacks and security quizzes to assess employee awareness and identify areas where further training is required, can be effective.
To truly educate employees on risks, it’s essential to move beyond compliance and build a cybersecurity culture throughout the organisation. This can involve setting organisation-wide security KPIs that cascade from the CEO down to every employee, promoting accountability and transparency. Creating an environment where employees feel comfortable reporting security concerns is critical for early threat detection and mitigation.
Policies. Clear security policies and enforcement are essential for ensuring that employees understand their roles within the broader security framework, including responsibilities on strong password use, secure data handling, and prompt incident reporting. Implementing the principle of least privilege, which restricts access based on specific roles, mitigates potential harm from insider threats and inadvertent data exposure. Policies should evolve through routine security audits, including technical assessments and evaluations of employee protocol adherence, which will help organisations with a swifter identification of vulnerabilities and to take the necessary corrective actions.
However, despite the best efforts, breaches do happen – and this is where a well-defined incident response plan, that is regularly tested and updated, is crucial to minimise the damage. This requires every employee to know their roles and responsibilities during a security incident.
Tech Expansion Leading to Cyber Complexity
Cloud. Initially hesitant to transition essential workloads to the cloud, the BFSI industry has experienced a shift in perspective due to the rise of inventive SaaS-based Fintech tools and hybrid cloud solutions, that have created new impetus for change. This new distributed architecture requires a fresh look at cyber measures. Secure Access Service Edge (SASE) providers are integrating a range of cloud-delivered safeguards, such as FWaaS, CASB, and ZTNA with SD-WAN to ensure organisations can securely access the cloud without compromising on performance.
Data & AI. Data holds paramount importance in the BFSI industry for informed decision-making, personalised customer experiences, risk assessment, fraud prevention, and regulatory compliance. AI applications are being used to tailor products and services, optimise operational efficiency, and stay competitive in an evolving market. As part of their technology modernisation efforts, 47% of BFSI institutions are refining their data and AI strategies. They also acknowledge the challenges associated – and satisfying risk, regulatory, and compliance requirements is one of the biggest challenges facing BFSI organisations in the AI deployments.
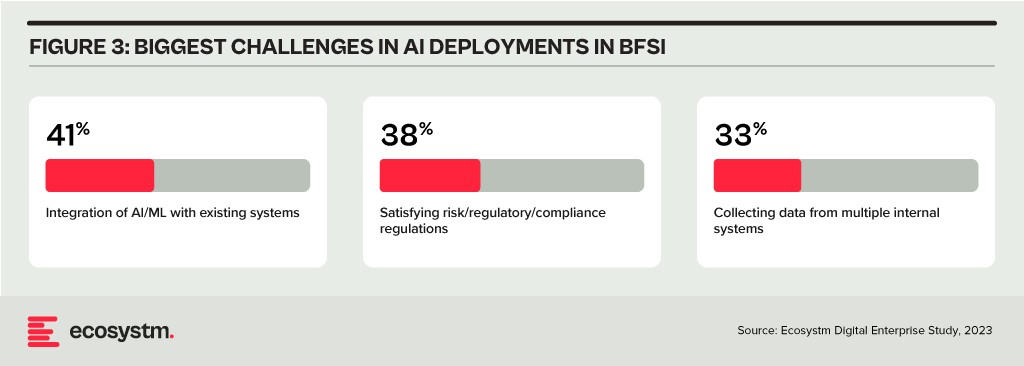
The rush to experiment with Generative AI and foundation models to assist customers and employees is only heightening these concerns. There is an urgent need for policies around the use of these emerging technologies. Initiatives such as the Monetary Authority of Singapore’s Veritas that aim to enable financial institutions to evaluate their AI and data analytics solutions against the principles of fairness, ethics, accountability, and transparency (FEAT) are expected to provide the much-needed guidance to the industry.
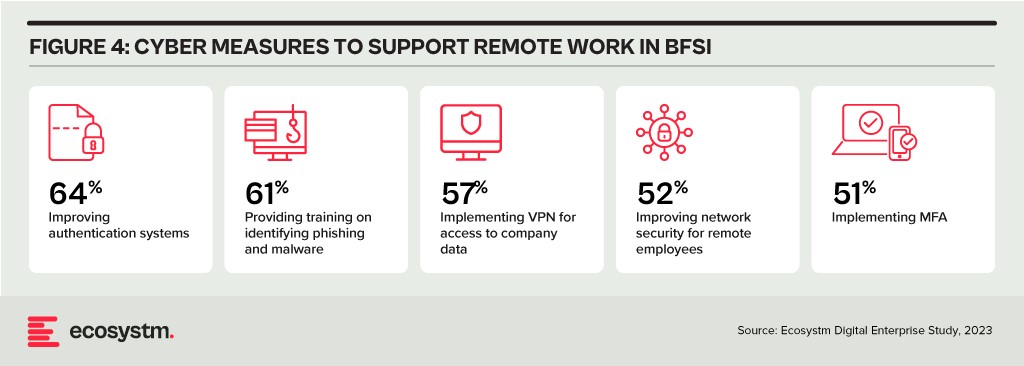
Digital Workplace. As with other industries with a high percentage of knowledge workers, BFSI organisations are grappling with granting remote access to staff. Cloud-based collaboration and Fintech tools, BYOD policies, and sensitive data traversing home networks are all creating new challenges for cyber teams. Modern approaches, such as zero trust network access, privilege management, and network segmentation are necessary to ensure workers can seamlessly but securely perform their roles remotely.
Looking Beyond Technology: Evaluating the Adequacy of Compliance-Centric Cyber Strategies
The BFSI industry stands among the most rigorously regulated industries, with scrutiny intensifying following every collapse or notable breach. Cyber and data protection teams shoulder the responsibility of understanding the implications of and adhering to emerging data protection regulations in areas such as GDPR, PCI-DSS, SOC 2, and PSD2. Automating compliance procedures emerges as a compelling solution to streamline processes, mitigate risks, and curtail expenses. Technologies such as robotic process automation (RPA), low-code development, and continuous compliance monitoring are gaining prominence.
The adoption of AI to enhance security is still emerging but will accelerate rapidly. Ecosystm research shows that within the next two years, nearly 70% of BFSI organisations will have invested in SecOps. AI can help Security Operations Centres (SOCs) prioritise alerts and respond to threats faster than could be performed manually. Additionally, the expanding variety of network endpoints, including customer devices, ATMs, and tools used by frontline employees, can embrace AI-enhanced protection without introducing additional onboarding friction.
However, there is a need for BFSI organisations to look beyond compliance checklists to a more holistic cyber approach that can prioritise cyber measures continually based on the risk to the organisations. And this is one of the biggest challenges that BFSI CISOs face. Ecosystm research finds that 72% of cyber and technology leaders in the industry feel that there is limited understanding of cyber risk and governance in their organisations.
In fact, BFSI organisations must look at the interconnectedness of an intelligence-led and risk-based strategy. Thorough risk assessments let organisations prioritise vulnerability mitigation effectively. This targeted approach optimises security initiatives by focusing on high-risk areas, reducing security debt. To adapt to evolving threats, intelligence should inform risk assessment. Intelligence-led strategies empower cybersecurity leaders with real-time threat insights for proactive measures, actively tackling emerging threats and vulnerabilities – and definitely moving beyond compliance-focused strategies.

There are two types of organisations – those that know that they have had a cybersecurity breach and those that don’t. With ransomware accounting for a rapidly growing proportion of breaches, not knowing you have been breached is less likely. In the last two months, we have seen a series of devastating ransomware attacks. These have included attacks on critical infrastructure, Colonial Pipeline and JBS, and the more recent supply chain attack on Kaseya, infecting its customers’ customers with ransomware. We’ve also seen an increase in attacks on soft targets such as schools and hospitals.
What is ransomware? Well, it’s a type of malware that specialises in encrypting the victim’s data and demands a ransom for a decryption key which may or may not work. If the victim fails to pay, their data could be sold or published online. More worryingly, if the victim pays, their data could still be sold or published online, prolonging the agony. Common ransomware families include REvil, Locky, Wannacry, Cerber, NotPetya, Maze and Darkside.
Why is Ransomware Becoming more Widespread?
Increased digitisation, remote working, accelerated adoption of cloud computing and growth in IoT devices, have expanded the attack surface for threat actors – offering more vulnerabilities that can be exploited. Launching a ransomware attack is a relatively easy and low-risk way to make money for cyber-criminals. Threat actors are usually outside the jurisdiction where the attack takes place and are typically protected by the absence of extradition treaties between the country where the crime occurred and the country from where the attack was launched. As well as posing a remarkably low risk to the attacker the rewards from a successful ransomware attack are potentially very large. Ransomware as a service (RaaS) kits can be purchased on the dark web for a few hundred dollars and if used repeatedly are likely to find at least one victim. Cryptocurrencies such as bitcoin make it virtually impossible for law enforcement authorities to track ransom payments. Consequently, the rapid growth in ransoms combined with the increasing risk of successful ransomware attacks is leading to banks stocking up on bitcoin. This allows their customers to quickly pay ransoms.

How to Mitigate the Risks?
Companies will not be able to completely eliminate the risk of ransomware attacks. They can, however, mitigate the risk of these attacks with a zero-trust approach to cybersecurity, renewed focus on training and awareness programs, and well-prepared and rehearsed incident response plans.
Rigorously applying the principle of least privilege will make it harder for threat actors to gain the credentials that they need to move laterally within systems and networks. Segmenting networks and isolating workloads will limit the blast radius of attacks. Training and awareness campaigns will make employees less likely to download malware via phishing attacks or other social engineering activities. Ensuring that all sensitive data is classified and encrypted will make double extortion more difficult – a miserable scenario where the victim pays a ransom for a decryption key and is then asked to pay a further ransom for the dubious promise that stolen data will not be leaked.
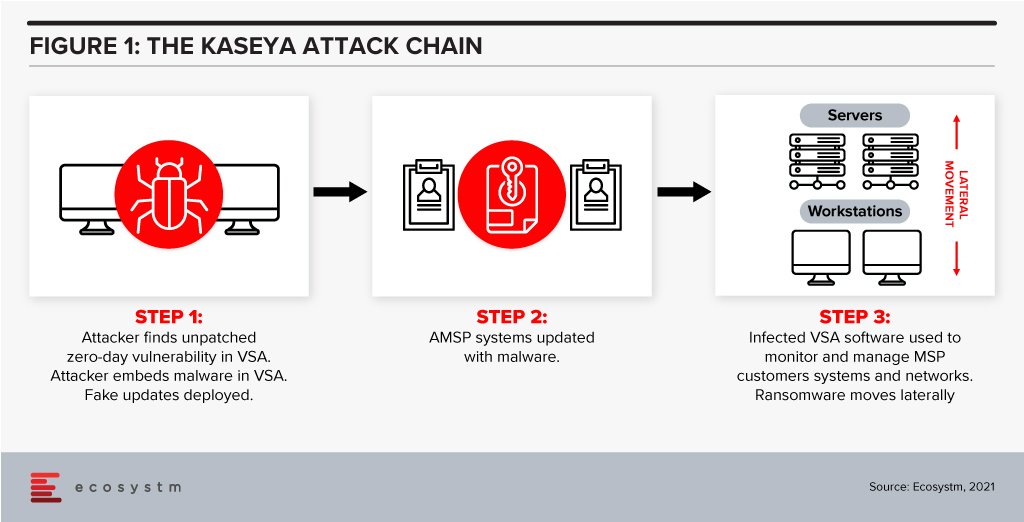
Protecting against supply chain ransomware attacks, such as the Kaseya breach, is fiendishly difficult. In the case of Kaseya, attackers identified a zero-day vulnerability in its VSA IT management and monitoring tool. An update was then infected with ransomware and shared with managed service providers, who, in turn infected their customers with the ransomware.
Rehearsed incident response plans that prepare for a successful ransomware attack are essential controls against such threats. A critical component of such a plan is backup and recovery. Backups are increasingly being targeted in well-orchestrated attacks so companies must find ways of ensuring that their data is stored in at least one immutable destination. This means that they can recover quickly – often almost instantly if the process is automated.
If companies follow cybersecurity best practices such as those outlined above, they should be able to manage ransomware risk and the misery associated with these attacks. If a ransomware attack occurs, well-prepared companies will be able to recover rapidly and be comfortable in the knowledge that the data which has been stolen is of little or no value to the attackers.

Ecosystm recently partnered with Asavie to conduct a study on the opportunity and outlook for the “Branch of One“. The results of the study make us question whether organisations’ mobile security strategies are appropriate for the evolving business priorities, the ever-changing threat landscape, and a seamless employee experience.
To answer this question, organisations will need to examine their security frameworks.
COVID-19 has forced organisations to realise that cybersecurity is not only a business enabler – it is a business prerequisite. Our research shows that businesses world-wide no longer see the pandemic as something that we need to get through to get back to “business as usual”. Most acknowledge that remote working and access from anywhere will be the new normal for many employees and that means they need to revisit and reprioritise their spending and their focus.
In many cases, existing procedures and policies are not sufficient to cover this new working environment – and often the policies have not been clearly communicated to all employees. Moreover, many organisations still rely on legacy WAN technologies that make secure and flexible access difficult – something that my colleague, Tim Sheedy touched upon in his recent blog post.
The choice of WAN technology is an important part of any mobile security strategy, but so is the approach to securing endpoints on the WAN and – what is perhaps the weakest link – the behaviour of employees.
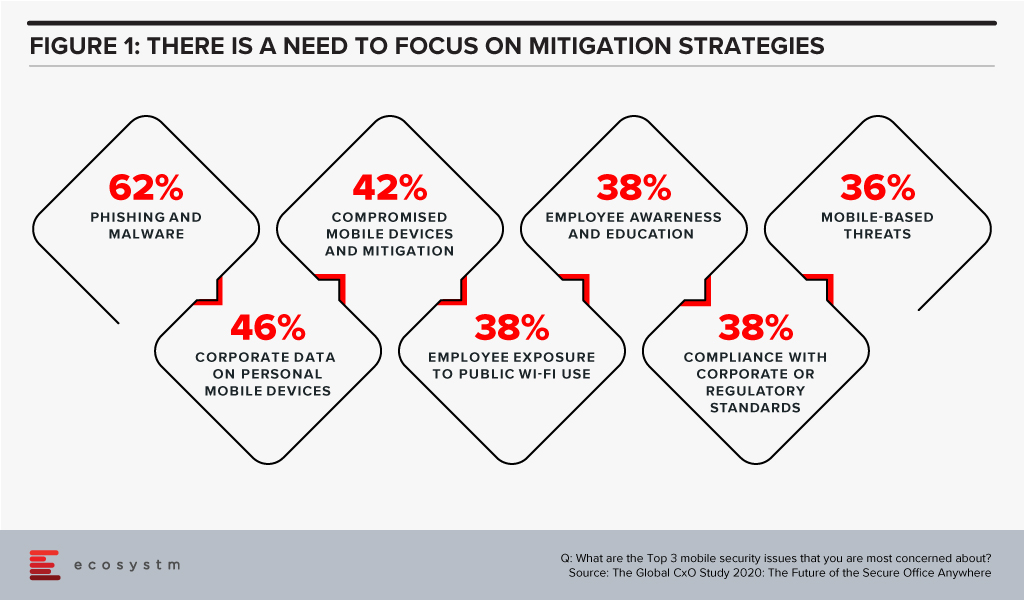
The Global CxO Study 2020: The Future of Secure Office Anywhere showed us that when it came to mobile security, organisations were mostly worried about phishing and malware – but 4 out of the top 5 mobile security concerns involved human error and failure to follow corporate IT security policies and guidelines (Figure 1).
Time to Evaluate New Mobile Security Features
This highlights the importance of a couple of “security features” that many IT organisations still tend to overlook – convenience and ease-of-use. When employees ignore IT policies, bypass security steps, use unsanctioned personal devices to process work data etc., they tend to do so for mainly one reason: because it is convenient for them. Employees just want to get the work done and following security protocols, making sure that devices have the right security software installed etc. is simply seen as too cumbersome or as slowing down the work process.
To counter this, ease-of-use and convenience need to an integral part of any security framework – especially when employees are no longer working in the office. IT managers tend to be a bit ego-centric when they think of these terms, i.e. for them ease-of-use relates to their experience in implementing and running the systems, but they really need to be extending the ease to their users – the employees – as well.
This is where Branch of One comes to the fore. It offers the convenience of employees not having to install or connect software or hardware on the mobile device and it allows administrators to easily scale and manage their mobile security framework. Security frameworks do not have to be in the way of getting the work done. Branch of One shows us that comprehensive mobile security can be nearly seamless.
Download the report based on ‘The Global CxO Study 2020: The Future of the Secure Office Anywhere’, conducted by Ecosystm on behalf of Asavie. The report presents the key findings of the study and analyses the market perceptions of Office Anywhere and the need for a ‘Branch of One’, which will be the foundation of enterprise mobile security in the future.

Organisations across the globe, are facing disruption on a scale never seen before, and are urgently seeking ways of remaining viable. Predictably, cybersecurity is a secondary concern and is often handled reactively. To make matters worse, a chronic cybersecurity skills shortage is being made much more severe by the crisis.
Remote working has reached unprecedented levels as organisations try hard to keep going. This is massively expanding the attack surface for cyber criminals, weakening security and leading to a cybercrime pandemic. Hacking activity and phishing, inspired by the COVID-19 crisis, are growing rapidly. Containing and suppressing this cybercrime pandemic is proving to be almost impossible.
Remote working intensifies known threats posed by phishing and ransomware. More alarming are the distinctive cybersecurity vulnerabilities associated with home working including reliance on home Wi-Fi, increased use of unpatched VPNs and devices, and the exponential growth of network access points. These vulnerabilities increase the likelihood of a breach enormously.
Corporate IT is in a very challenging position. It needs to ensure that organisations can operate in a way that they have never operated before, while ensuring that their assets are secure – a very difficult, if not an impossible task for which there is no precedent.
Some important cybersecurity considerations, during and after the COVID-19 pandemic include:
Re-enforce Basic Cyber Hygiene
As massive numbers of people work from home, basic cyber hygiene becomes more critical than ever before. Organisations must maintain awareness of security threats among employees, ensure security policies are being followed and be certain that corporate software is being updated and patched on time. With a dispersed workforce, these basic practices are more challenging, and training becomes more critical. Phishing attacks are often the primary attack vector for malicious actors, so employees must be able to identify these attacks. They increasingly exploit shortages of goods such as protective equipment and sometimes claim to offer official information relating to COVID-19.
Remote employees often access sensitive business data through home Wi-Fi networks that will not have the same security controls – such as firewalls – that are used in offices. There is more connectivity from remote locations, which requires greater focus on data privacy, and hunting for intrusions from a much larger number of entry points.
Place More Focus on Endpoint Security
The unprecedented switch to remote working is radically increasing the number of vulnerable endpoints. Given that endpoints are located at a distance from corporate premises, it is frequently difficult for IT departments to configure endpoint systems and install necessary security software.
It is vital to assess the security posture of all endpoints connecting to the corporate network. This practice enables an organisation to determine whether or not an endpoint requesting to access internal resources meets security policy requirements. It requires the ability to monitor and enforce policy across all devices, while making onboarding and offboarding seamless.
It is essential that endpoint solutions can be rapidly deployed for remote workers, as needed on both personal and corporate devices. Devices used for remote work need much more than the basic antivirus and antispyware protection. Multi-factor authentication (MFA) and on-board endpoint detection and response (EDR) capabilities are crucial.
Be More Selective About How and When Video Conferencing and Collaboration Platforms are Used
Since lockdowns spread around the world, the use of video conferencing and collaboration tools has grown beyond the wildest expectations of suppliers of these tools. The extraordinary growth of Zoom has made it a target for attackers. Many security vulnerabilities have been discovered with Zoom such as, a vulnerability to UNC path injection in the client chat feature, which allows hackers to steal Windows credentials, keeping decryption keys in the cloud which can potentially be accessed by hackers and gives the ability for trolls to ‘Zoombomb’ open and unprotected meetings. Zoom has so far managed to augment its security features in part by its recent acquisition of Keybase, a secure messaging service.
Switching to an alternative video conferencing platform will not necessarily offer greater levels of security as privacy is typically not a strength of any collaboration platform. Collaboration platforms tend to tread a fine line between a great experience and security. Too much security can cause performance and usability to be impacted negatively. Too little security, as we have seen, allows hackers to find vulnerabilities. If data privacy is critical for a meeting, then perhaps collaboration platforms should not be used, or organisations should not share critical information on them.
Protect all Cloud Workloads
In today’s remote working paradigm, cloud computing is being used more than ever. This frequently exposes organisations to risks that are not adequately mitigated.
Organisations typically need to manage a mix of on-premises technology together with multiple clouds, which are often poorly integrated. These complexities are compounded by the increasing risk from cyberattacks associated with cloud migration and hybrid cloud implementations. In cloud environments, the leading cybersecurity risks include insecure interfaces and APIs, data breaches and data loss, unauthorised access, DDoS attacks, and a lack of a unified view of assets.
Protection requirements for securing hybrid multicloud environments are evolving rapidly. In addition to tightening up endpoint security, organisations must also place greater emphasis on cloud workload protection. Cloud security solutions need to offer a unified and consistent view across all physical machines, virtual machines, serverless workloads and containers, used by an organisation.
Amend Incident Response Plans
It is the containment of breaches that often determines the success of security policies and procedures. Basic cyber hygiene as well as changes to IT architecture, such as micro segmentation, play an essential role in breach containment. But incident response plans also need to be made relevant to the current pandemic scenario.
Employees and IT teams are now working in a completely different environment than envisaged by most incident response plans. Existing plans may now be obsolete. At the very least, they will need to be modified. Usually, incident response plans are designed to respond to threats when most employees are operating in a corporate environment. This clearly needs to change. Employees need to be trained in the updated plan and know how to reach support if they believe that a security breach has occurred in their remote location.
Critically, new alert and warning systems need to be established, which can be used by employees to warn of threats as well as to receive information on threats and best practices.
Organisations are struggling to keep the lights on. In this battle to remain operational, cybersecurity has been taking a back seat. This cannot last for long as the deluge of new vulnerabilities is creating easy pickings for attackers. Cyber hygiene, endpoint security, cloud security, security policies and incident response plans must be continually reviewed.
Click here to download the full report ?