Qualtrics, a leading global Voice of Customer (VoC) provider, held its annual X4 conference in May, at the ICC in Sydney. The event included an exclusive media lunch and focused on Qualtrics’ latest announcements and product enhancements, many of which were first unveiled at its US event in March.
The conference combined insights into the company’s technology roadmap with real-world customer success stories, featuring organisations such as KFC, ServiceNow, David Jones, Hilton, and others.
In a world dominated by AI agents, the opportunity lies in building real human connections. The challenge, however, is to do this at scale. Empowering people with AI agents, rather than replacing them, can improve efficiency while also creating space for more empathetic, human-centred interactions, the vendor argues. The theme of building connections and making every connection count came through loud and clear and was weaved through the product announcements.
Here are my key takeaways from attending the conference.
Culture is Key
It was refreshing to see culture take centre stage at a vendor briefing – a critical pillar for CX success that’s too often overlooked in technology conversations.
While technology is critical to enable a successful CX practice and continuously improve customer experience, building a culture of customer centricity must be the foundation for technology to be successful.
It’s critical to break down internal silos to unify data across the organisation and democratise insights. With customer feedback now coming into the organisation through various channels (surveys, calls, emails, social media, etc.), GenAI enables organisations to create a holistic understanding of experiences across all channels and touchpoints. Likewise, that data needs to be shared with the right internal teams to enable continuous improvement opportunities. For that to happen, organisations need to develop a culture of customer centricity and break out of their silo-centric mindset.
Qualtrics Experience Agents
No surprise, Agentic AI has made it into the world of customer feedback with Brad Anderson, President – Products, User Experience, and Engineering, introducing Qualtrics Experience Agents.
Qualtrics has started to develop AI agents and is slowly embedding this capability into the platform. Think about closing the loop with customers, automating small tasks, and proactively identifying issues before we hear about them.
The Experience Agents can respond to customers during the survey process or can be embedded into the digital experience to address problems in real time. Closing the loop with customers, across surveys and other service requests, can be a timely and resource intense undertaking. Qualtrics’ autonomous agents can close the loop with 100% of customers, automatically responding in real time, building empathy and making your customers feel heard.
It’s still early days for Qualtrics’ Experience Agents and I look forward to seeing tangible outcomes of customer implementations. I’m sure we’ll hear more about this over the coming months!
Surveys Just Got Smarter
Qualtrics introduced “agentified” surveys, a new way to respond to verbatim survey feedback, adjust follow up questions accordingly, and turn surveys into conversations.
This is an evolution of what’s referred to as verbatim probing. They represent a new way of getting actionable feedback from customers through AI enabled and adaptive questioning during a survey.
The new technology enhances the insight quality and aims to build empathy with customers. Verbatim responses become richer in value and Qualtrics reports a slight increase in survey completion rates. The aim is to turn surveys into conversations, leaving customers feeling heard and building stronger connections.
Despite the adoption of unsolicited feedback as a source of customer insights, surveys still represent the foundation for any VoC program, and they’re not going to go away any time soon. Enhancing survey capabilities while adding operational and unsolicited feedback to the mix will be key to establishing a deeper understating of customer experience and identifying improvement opportunities.
Show Me the Money
Qualtrics highlights the importance of linking CX initiatives to business outcomes and results to demonstrate ROI and gain buy-in and continued support from key stakeholders.
When VoC programs were first introduced, the main challenge for most organisations was gathering customer feedback. Once that hurdle was overcome – thanks to technology – the next challenge became converting raw data into meaningful insights, especially with the addition of unstructured data sources.
The focus then shifted from insights to identifying and driving action. Mature organisations are now at the stage of tangibly linking CX results to business outcomes and showcasing ROI. Quantifying business impact is an essential step in enabling CX success, yet it is often neglected.
Most organisations are still working on building robust Insights-to-Action frameworks and translating insights into tangible action; efforts often hindered by limited collaboration and a lack of customer-centric culture. For more mature organisations, the challenge now lies in clearly demonstrating the business outcomes and ROI of their CX programs.
Other Announcements
Qualtrics Assist. Alongside other technology giants, Qualtrics’ ‘Assist’ solution is an easy way to query the data in a natural language style, i.e. asking data questions to find insights. This is particularly important for larger data sets that comprise survey and unsolicited feedback, as it significantly speeds up the insight generation process. Analysis that used to take days or weeks, can now be completed in minutes or seconds.
Qualtrics Edge. Qualtrics has started to introduce synthetic data to its Research product suit. It’s a niche market at this stage but certainly growing in popularity as utilising synthetic data, panels and personas not only significantly speeds up the research process but also reduces cost. I’m interested to see market uptake for this. While it’s not new per se, organisations still need to overcome the “trust” hurdle to fully embrace synthetic data and research.
Customer Service and VoC: Boundaries Blur Further
While AI agents have dominated contact centre conversations in recent months, Qualtrics is one of the few VoC vendors now introducing Agentic AI with its Experience Agents.
This is particularly relevant for the digital experience space, where a variety of vendors are offering solutions. Qualtrics’ Experience Agents can detect signs of frustration and rage clicking during digital sessions and proactively engage to close the loop in real time.
It will be interesting to see how the growing number of agents from different vendors ultimately work together in a coordinated way to enhance experiences, rather than introduce new points of friction.
The contact centre has long been a goldmine for customer experience data and insights. Today, tapping into conversational data has become an open field for vendors across VoC, contact centre, and conversational intelligence categories. While this brings innovation, it also complicates decision-making for technology buyers. With vendors from different backgrounds offering overlapping capabilities, often to different internal stakeholders, organisations risk ending up with complex, costly tech stacks.
That said, it’s encouraging to see Qualtrics continue to develop and embed GenAI and Agentic AI into its platform. As a leader in the CX space, it’s setting a high bar for the rest of the market.

At the Agentforce World Tour in Singapore, Salesforce presented their vision for Agentic AI – showcasing how they’re helping customers stay ahead of rapid technological change and unlock stronger business outcomes with speed, trust, and agility.
Ecosystm Advisors, Ullrich Loeffler, Sash Mukherjee, Achim Granzen, and Manish Goenka share their take on Salesforce’s announcements, demos, and messaging, highlighting what resonated, what stood out, and what it means for the future.
Click here to download “Agentforce World Tour: Highlights from Singapore” as a PDF.
What truly stood out in Salesforce’s messaging?
ULLRICH LOEFFLER, CEO & Co-Founder
What stood out at the Salesforce event was their pragmatic, integrated approach to scaling AI. They made it clear AI isn’t plug-and-play, emphasising the complexity and cost involved in what they call ‘self-plumbing’ AI – spanning infrastructure, data management, model development, governance, and application integration. Their answer is a unified platform that lowers costs, accelerates time to market, and reduces risk by removing the need to manage multiple disconnected tools. This seamless environment tackles the real challenge of building and running a layered AI stack.
Equally notable is their view of Agentic AI as a capability refined through iteration, not a sudden overhaul. By urging businesses to start with the right use cases for faster adoption, less disruption, and tangible impact, they show a realistic grasp of enterprise change.
Salesforce offers a clear, practical path to AI: simplifying complexity through integration and driving adoption with measured, value-focused steps.
SASH MUKHERJEE, VP Industry Insights
What truly stood out at the Salesforce event was their unwavering commitment to Trust. They understand that AI agents are only as reliable as the data they use, and they’ve built their platform to address this head-on. Salesforce emphasises that building trusted AI means more than just powerful models; it requires a secure and well-governed data foundation. They highlighted how their platform, with 25 years of embedded security, ensures data resilience, protects sensitive information during development and testing, and provides robust visibility into how AI interacts with your data.
A key assurance is their Trust Layer, a unique innovation that safeguards your data when interacting with AI models. This layer automatically masks sensitive data, ensures zero data retention by LLM providers, and detects harmful language. This means organisations can leverage GenAI’s power without compromising sensitive information.
Ultimately, Salesforce is empowering organisations to confidently deploy AI by making trust non-negotiable, ensuring organisational data is used responsibly and securely to drive real business value.
How does Salesforce differentiate their approach to Agentic AI?
ACHIM GRANZEN, Principal Advisor
Salesforce’s focus on Agentic AI focus stands out for its clarity and depth. The Agentforce platform takes centre stage, demonstrating how clients can now build Agentic AI with little or no code and deploy agents seamlessly across the Salesforce environment.
But beyond the polished demos and compelling customer stories, the most critical takeaway risked being overlooked: Agentforce is not a standalone capability. It’s tightly integrated with Data Cloud and the broader Salesforce platform. That layered architecture is more than just a technical decision; it’s what ensures every AI agent is governed, auditable, and constrained to what’s been provisioned in Data Cloud. It’s the foundational safeguard that makes Agentic AI viable in the enterprise.
And that’s the message that needs greater emphasis. As organisations move from experimentation to real-world deployment, trust and control become just as vital as ease of use. Salesforce’s architecture delivers both – and that balance is a key differentiator in the crowded enterprise AI space.
MANISH GOENKA, Principal Advisor
Salesforce has moved beyond passive AI assistance to autonomous agents that can take meaningful action within trusted boundaries. Rather than focusing solely on chat-based copilots, Salesforce emphasises intelligent agents embedded into business workflows, capable of executing tasks like claims processing or personalised service without human intervention.
What sets Salesforce apart is how deeply this vision is integrated into their platform. With Einstein Copilot and Copilot Studio, customers can build their own cross-system agents, not just those limited to Salesforce apps. And by enabling partners to create and monetise agents via AppExchange, Salesforce is building a full-fledged AI ecosystem, positioning themselves as a platform for enterprise AI, not just a CRM.
Trust is a cornerstone of this approach. Salesforce’s focus on governance, auditability, and ethical AI ensures that Agentic AI is not only powerful, but also secure and accountable – key concerns as agents become more autonomous.
In a crowded AI space, Salesforce stands out by offering a grounded, scalable vision of Agentic AI, anchored in real use cases, platform extensibility, and responsible innovation.
Where are Salesforce’s biggest growth opportunities in APAC?
MANISH GOENKA
Salesforce has significant growth opportunities across Asia Pacific, with Singapore playing a pivotal role in its regional strategy. The company’s USD 1 billion investment and the launch of their first overseas AI research hub firmly position Singapore as more than just a sales market. It becomes a core engine for product innovation and a key driver of Salesforce’s long-term AI leadership.
Across the region, public sector transformation and SME digitisation represent major areas of opportunity. Salesforce’s secure and compliant Government Cloud is well suited to support Smart Nation goals and modernise public digital services. At the same time, governments are actively pushing SME digitisation, creating demand for scalable, modular platforms that can grow from basic CRM solutions to AI-enabled automation.
Sustainability is also emerging as a strong growth vector. As ESG reporting becomes commonplace in more markets, tools like Net Zero Cloud are well positioned to help businesses meet compliance requirements and improve data transparency.
Finally, the rapidly expanding ecosystem of certified professionals and ISV partners across Asia Pacific is enabling faster, more localised implementations. This grounds Salesforce’s capabilities in local context, accelerating time to value and delivering business outcomes that are tailored to the region’s diverse needs.
What does the Informatica acquisition mean for Salesforce’s AI strategy?
ACHIM GRANZEN
The planned acquisition of Informatica is a strategically important move that completes Salesforce’s Agentforce narrative. At the World Tour, Agentforce was positioned as the future of enterprise AI, allowing organisations to build and deploy autonomous agents across the Salesforce ecosystem. But some lingering concerns remained around how deeply Data Cloud could handle governance, especially as AI agents begin making decisions and executing tasks without human oversight.
Informatica answers that question. With proven tools for data quality, lineage, and policy enforcement, Informatica brings a level of governance maturity that complements Salesforce’s ambition. Its integration into Data Cloud strengthens the trust layer that underpins Agentforce and reinforces Salesforce’s positioning as an enterprise-grade AI platform.
Of course, there are broader implications too. Salesforce will gain access to Informatica’s installed base, potentially opening up cross-sell opportunities. And there are questions to resolve, such as how Informatica will operate as a product line within the larger Salesforce ecosystem.
But the core value of the deal is clear: by bringing Informatica’s governance expertise into the fold, Salesforce can significantly accelerate its ability to deliver trusted, production-ready AI at scale. From a risk and compliance standpoint, that governance capability may prove to be the most valuable part of the acquisition.
What will define Salesforce’s next chapter of growth in APAC?
SASH MUKHERJEE
Just as Salesforce is driving an integrated enterprise platform from the CRM and customer experience lens, competitors (and partners) are taking a similar platform-centric approach from other functional vantage points – whether it’s HR (like Workday), Finance (like Oracle), or IT (like ServiceNow). In fast-growing, cost-sensitive markets across APAC, competing on price alone won’t be sustainable, especially with strong regional players offering leaner, localised alternatives.
To win, Salesforce must adopt a nuanced strategy that goes beyond product breadth. This means addressing local economic realities – offering right-sized solutions for businesses at different stages of digital maturity – while consistently reinforcing the long-term value, resilience, and global standards that set Salesforce apart. Their differentiators in data security, compliance, and ecosystem depth must be positioned not as add-ons, but as essential foundations for future-ready growth.
More flexible entry points – whether modular offerings, usage-based pricing, or vertical-specific bundles – can reduce friction and make the platform more accessible. At the same time, strengthening local partnerships with ISVs, system integrators, and government bodies can help tailor offerings to market-specific needs, ensuring relevance and faster implementation.
Ultimately, Salesforce’s growth across APAC will depend on their ability to balance global strengths with local agility.
ULLRICH LOEFFLER
Salesforce is well positioned to lead in AI-driven transformation, but doing so will require evolving their sales approach to match the complexity and expectations of today’s enterprise buyers. With a strong foundation selling to marketing and customer leaders, the company now has an opportunity to deepen engagement with CIOs and CTOs, reframing themselves not just as a CRM provider, but as a full-spectrum enterprise platform.
Traditional sales reps who excel at pitching features to business users are no longer enough. Selling AI – particularly agentic, autonomous AI – demands sales professionals who can link technical capabilities to strategic outcomes and lead conversations around risk, compliance, and long-term value.
To sustain their leadership, Salesforce will need to invest in a new generation of sales talent: domain-fluent, consultative, and able to navigate complex, cross-functional buying journeys.

In AI’s early days, enterprise leaders asked a straightforward question: “What can this automate?” The focus was on speed, scale, and efficiency and AI delivered. But that question is evolving. Now, the more urgent ask is: “Can this AI understand people?”
This shift – from automation to emotional intelligence – isn’t just theoretical. It’s already transforming how organisations connect with customers, empower employees, and design digital experiences. We’re shifting to a phase of humanised AI – systems that don’t just respond accurately, but intuitively, with sensitivity to mood, tone, and need.
One of the most unexpected, and revealing, AI use cases is therapy. Millions now turn to AI chat tools to manage anxiety, process emotions, and share deeply personal thoughts. What started as fringe behaviour is fast becoming mainstream. This emotional turn isn’t a passing trend; it marks a fundamental shift in how people expect technology to relate to them.
For enterprises, this raises a critical challenge: If customers are beginning to turn to AI for emotional support, what kind of relationship do they expect from it? And what does it take to meet that expectation – not just effectively, but responsibly, and at scale?
The Rise of Chatbot Therapy
Therapy was never meant to be one of AI’s first mass-market emotional use cases; and yet, here we are.
Apps like Wysa, Serena, and Youper have been quietly reshaping the digital mental health landscape for years, offering on-demand support through chatbots. Designed by clinicians, these tools draw on established methods like Cognitive Behavioural Therapy (CBT) and mindfulness to help users manage anxiety, depression, and stress. The conversations are friendly, structured, and often, surprisingly helpful.
But something even more unexpected is happening; people are now using general-purpose AI tools like ChatGPT for therapeutic support, despite them not being designed for it. Increasingly, users are turning to ChatGPT to talk through emotions, navigate relationship issues, or manage daily stress. Reddit threads and social posts describe it being used as a therapist or sounding board. This isn’t Replika or Wysa, but a general AI assistant being shaped into a personal mental health tool purely through user behaviour.
This shift is driven by a few key factors. First, access. Traditional therapy is expensive, hard to schedule, and for many, emotionally intimidating. AI, on the other hand, is always available, listens without judgement, and never gets tired.
Tone plays a big role too. Thanks to advances in reinforcement learning and tone conditioning, models like ChatGPT are trained to respond with calm, non-judgmental empathy. The result feels emotionally safe; a rare and valuable quality for those facing anxiety, isolation, or uncertainty. A recent PLOS study found that not only did participants struggle to tell human therapists apart from ChatGPT, they actually rated the AI responses as more validating and empathetic.
And finally, and perhaps surprisingly, is trust. Unlike wellness apps that push subscriptions or ads, AI chat feels personal and agenda-free. Users feel in control of the interaction – no small thing in a space as vulnerable as mental health.
None of this suggests AI should replace professional care. Risks like dependency, misinformation, or reinforcing harmful patterns are real. But it does send a powerful signal to enterprise leaders: people now expect digital systems to listen, care, and respond with emotional intelligence.
That expectation is changing how organisations design experiences – from how a support bot speaks to customers, to how an internal wellness assistant checks in with employees during a tough week. Humanised AI is no longer a niche feature of digital companions. It’s becoming a UX standard; one that signals care, builds trust, and deepens relationships.
Digital Companionship as a Solution for Support
Ten years ago, talking to your AI meant asking Siri to set a reminder. Today, it might mean sharing your feelings with a digital companion, seeking advice from a therapy chatbot, or even flirting with a virtual persona! This shift from functional assistant to emotional companion marks more than a technological leap. It reflects a deeper transformation in how people relate to machines.
One of the earliest examples of this is Replika, launched in 2017, which lets users create personalised chatbot friends or romantic partners. As GenAI advanced, so did Replika’s capabilities, remembering past conversations, adapting tone, even exchanging voice messages. A Nature study found that 90% of Replika users reported high levels of loneliness compared to the general population, but nearly half said the app gave them a genuine sense of social support.
Replika isn’t alone. In China, Xiaoice (spun off from Microsoft in 2020) has hundreds of millions of users, many of whom chat with it daily for companionship. In elder care, ElliQ, a tabletop robot designed for seniors has shown striking results: a report from New York State’s Office for the Aging cited a 95% drop in loneliness among participants.
Even more freeform platforms like Character.AI, where users converse with AI personas ranging from historical figures to fictional characters, are seeing explosive growth. People are spending hours in conversation – not to get things done, but to feel seen, inspired, or simply less alone.
The Technical Leap: What Has Changed Since the LLM Explosion
The use of LLMs for code editing and content creation is already mainstream in most enterprises but use cases have expanded alongside the capabilities of new models. LLMs now have the capacity to act more human – to carry emotional tone, remember user preferences, and maintain conversational continuity.
Key advances include:
- Memory. Persistent context and long-term recall
- Reinforcement Learning from Human Feedback (RLHF). Empathy and safety by design
- Sentiment and Emotion Recognition. Reading mood from text, voice, and expression
- Role Prompting. Personas using brand-aligned tone and behaviour
- Multimodal Interaction. Combining text, voice, image, gesture, and facial recognition
- Privacy-Sensitive Design. On-device inference, federated learning, and memory controls
Enterprise Implications: Emotionally Intelligent AI in Action
The examples shared might sound fringe or futuristic, but they reveal something real: people are now open to emotional interaction with AI. And that shift is creating ripple effects. If your customer service chatbot feels robotic, it pales in comparison to the AI friend someone chats with on their commute. If your HR wellness bot gives stock responses, it may fall flat next to the AI that helped a user through a panic attack the night before.
The lesson for enterprises isn’t to mimic friendship or romance, but to recognise the rising bar for emotional resonance. People want to feel understood. Increasingly, they expect that even from machines.
For enterprises, this opens new opportunities to tap into both emotional intelligence and public comfort with humanised AI. Emerging use cases include:
- Customer Experience. AI that senses tone, adapts responses, and knows when to escalate
- Brand Voice. Consistent personality and tone embedded in AI interfaces
- Employee Wellness. Assistants that support mental health, coaching, and daily check-ins
- Healthcare & Elder Care. Companions offering emotional and physical support
- CRM & Strategic Communications. Emotion-aware tools that guide relationship building
Ethical Design and Guardrails
Emotional AI brings not just opportunity, but responsibility. As machines become more attuned to human feelings, ethical complexity grows. Enterprises must ensure transparency – users should always know they’re speaking to a machine. Emotional data must be handled with the same care as health data. Empathy should serve the user, not manipulate them. Healthy boundaries and human fallback must be built in, and organisations need to be ready for regulation, especially in sensitive sectors like healthcare, finance, and education.
Emotional intelligence is no longer just a human skill; it’s becoming a core design principle, and soon, a baseline expectation.
Those who build emotionally intelligent AI with integrity can earn trust, loyalty, and genuine connection at scale. But success won’t come from speed or memory alone – it will come from how the experience makes people feel.

Asia is undergoing a digital renaissance. Central to this transformation is the rise of digital natives: companies born in the digital era, built on cloud infrastructure, powered by data, and guided by customer-centric agility. Unlike traditional businesses retrofitting technology onto old models, Asia’s digital natives have grown up with mobile-first architecture, software-as-a-service models, and a mindset of continuous iteration. They’re not merely disrupting — they are reshaping economies, industries, and even governance.
But we are seeing a new wave of change. The rise of Agentic AI – autonomous, multi-agent systems that handle workflows, decision-making, and collaboration with minimal human input – is set to redefine industries yet again. For digital natives, embracing Agentic AI is no longer optional. Those who adopt it will unlock unprecedented automation, speed, and scale. Those who don’t risk being leapfrogged by competitors operating faster, smarter, and more efficiently.
The path forward demands evolution and collaboration. Digital natives must upgrade their capabilities, while large tech vendors must shift from selling solutions to co-creating them with these agile players. Together, they can accelerate time-to-market and build future-ready ecosystems.
Reimagining Scale and Customer Experience
Asia’s digital natives have already proven that scale and localisation are not mutually exclusive. Grab, for instance, evolved from a ride-hailing app into Southeast Asia’s super-app by integrating services that reflect local habits, from hawker food delivery in Singapore to motorcycle taxis in Indonesia.
Rather than building physical infrastructure, they leverage platforms and cloud-native tools to reach millions at low marginal cost. AI has been their growth engine, powering hyper-personalisation and real-time responsiveness. Shopee dynamically tailors product recommendations, pricing, and even language options to create user experiences that feel “just for me.”
But with Agentic AI, the bar is rising again. The next leap isn’t just personalisation; it’s orchestration. Autonomous systems will manage entire customer journeys, dynamically adjusting pricing, inventory, and support across markets in real-time. Digital natives that embrace this will set new standards for customer responsiveness and operational scale.
To navigate this leap, co-creating AI solutions with tech partners will be crucial. Joint innovation will enable digital natives to move faster, build proprietary capabilities, and deliver richer customer experiences at scale.
Reshaping Work, Operations, and Organisational Models
Digital natives have long redefined how work gets done, breaking down silos and blending technology with business agility. But Agentic AI accelerates this transformation. Where AI once automated repetitive tasks, it now autonomously manages workflows across sales, legal, HR, and operations.
Tokopedia, for example, uses AI to triage customer queries, detect fraud, and optimise marketplace operations, freeing employees to focus on strategic work. This shift is reshaping productivity itself: traditional KPIs like team size or hours worked are giving way to outcome-driven metrics like resolution speed and value delivered.
With leaner but more impactful teams, digital natives are well-positioned to thrive. But success hinges on evolving workforce models. Upskilling employees to collaborate with AI is no longer optional. Data and AI literacy must be embedded across roles, transforming even non-technical teams into AI-augmented contributors.
This is where partnerships with big tech providers can unlock value. By co-developing workforce models, training frameworks, and governance structures, digital natives and vendors can accelerate AI adoption while keeping humans at the centre.
Unlocking New Ecosystems Through Data and Collaboration
Asia’s digital natives understand that data is more than an asset: it’s a strategic lever for building defensible moats and unlocking new ecosystems. Razorpay processes billions in payment data to assess SME creditworthiness, while LINE integrates messaging, payments, and content to deliver deeply personalised services.
What’s emerging is a shift from vendor-client dynamics to co-innovation partnerships. Flipkart’s collaboration with tech providers to deploy GenAI across customer support, logistics, and e-commerce personalisation is a prime example. By co-developing proprietary AI solutions – from multi-modal search to real-time inventory forecasting – Flipkart is turning its data ecosystem into a competitive advantage.
Agentic AI will only deepen this trend. As autonomous systems handle tasks once outsourced, firms are repatriating operations, creating resilient, data-governed ecosystems closer to consumers. This shift challenges traditional outsourcing models and aligns with Asia’s growing emphasis on data sovereignty and sovereign AI capabilities.
How Agentic AI Will Challenge Digital Natives
Even for Asia’s most agile players, Agentic AI presents new hurdles:
- Loss of Advantage. Without Agentic AI, digital natives risk falling behind as competitors unlock unprecedented automation and optimisation. What was once their competitive edge – speed and agility – could erode rapidly.
- Adaptation Costs. Transitioning to Agentic AI demands serious investment – in infrastructure, talent, and change management. Scaling autonomous systems is complex and resource-intensive.
- Talent Shift. Agentic AI will redefine traditional roles, enhancing employee contributions but also requiring massive upskilling and workflow redesigns. HR, sales, and operations teams must evolve or risk obsolescence.
Navigating these challenges will require digital natives to evolve not just technologically, but organisationally and culturally – and to seek partnerships that accelerate this transformation.
Digital Natives: From Disruptors to Co-Creators of Asia’s Future
Asia’s digital natives are no longer just disruptors; they are architects of the region’s digital economy. But as Agentic AI, data sovereignty, and ecosystem shifts reshape the landscape, they must evolve.
The future belongs to those who co-create. By partnering with large tech vendors, digital natives can accelerate innovation, scale faster, and solve the region’s biggest challenges, from inclusive finance to smart cities and sustainable mobility.

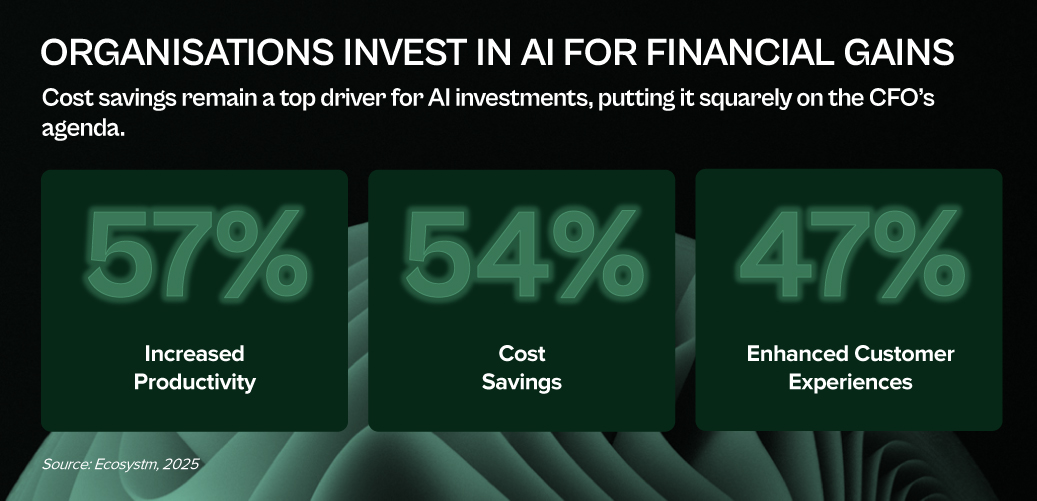
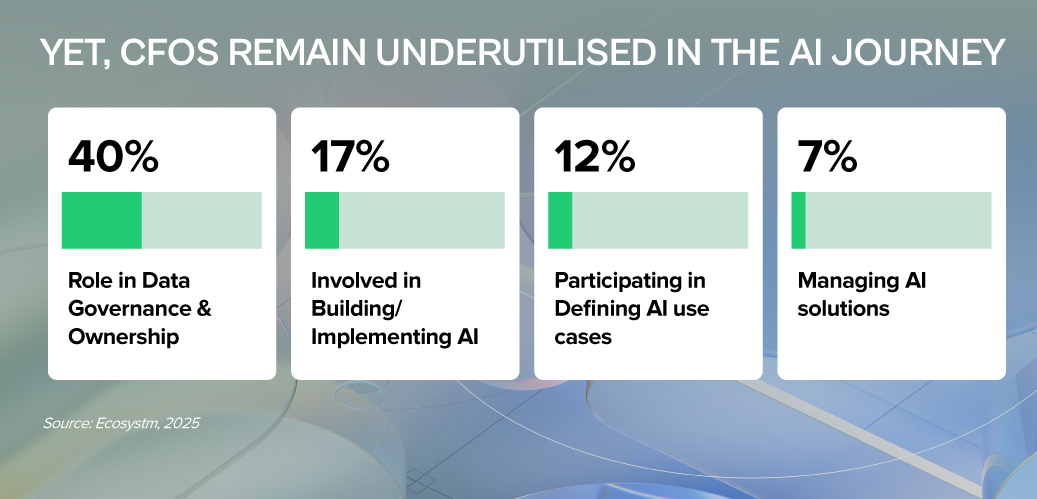
AI is not just reshaping how businesses operate — it’s redefining the CFO’s role at the centre of value creation, risk management, and operational leadership.
As stewards of capital, CFOs must cut through the hype and ensure AI investments deliver measurable business returns. As guardians of risk and compliance, they must shield their organisations from new threats — from algorithmic bias to data privacy breaches with heavy financial and reputational costs. And as leaders of their function, CFOs now have a generational opportunity to modernise finance, champion AI adoption, and build teams ready for an AI-powered future.
LEAD WITH RIGOUR. SAFEGUARD WITH VIGILANCE. CHAMPION WITH VISION.
That’s the CFO playbook for AI success.
Click here to download “AI Stakeholders: The Finance Perspective” as a PDF.
1. Investor & ROI Gatekeeper: Ensuring AI Delivers Value
CFOs must scrutinise AI investments with the same discipline as any major capital allocation.
- Demand Clear Business Cases. Every AI initiative should articulate the problem solved, expected gains (cost, efficiency, accuracy), and specific KPIs.
- Prioritise Tangible ROI. Focus on AI projects that show measurable impact. Start with high-return, lower-risk use cases before scaling.
- Assess Total Cost of Ownership (TCO). Go beyond upfront costs – factor in integration, maintenance, training, and ongoing AI model management.
Only 37% of Asia Pacific organisations invest in FinOps to cut costs, boost efficiency, and strengthen financial governance over tech spend.
2. Risk & Compliance Steward: Navigating AI’s New Risk Landscape
AI brings significant regulatory, compliance, and reputational risks that CFOs must manage – in partnership with peers across the business.
- Champion Data Quality & Governance. Enforce rigorous data standards and collaborate with IT, risk, and business teams to ensure accuracy, integrity, and compliance across the enterprise.
- Ensure Data Accessibility. Break down silos with CIOs and CDOs and invest in shared infrastructure that AI initiatives depend on – from data lakes to robust APIs.
- Address Bias & Safeguard Privacy. Monitor AI models to detect bias, especially in sensitive processes, while ensuring compliance.
- Protect Security & Prevent Breaches. Strengthen defences around financial and personal data to avoid costly security incidents and regulatory penalties.
3. AI Champion & Business Leader: Driving Adoption in Finance
Beyond gatekeeping, CFOs must actively champion AI to transform finance operations and build future-ready teams.
- Identify High-Impact Use Cases. Work with teams to apply AI where it solves real pain points – from automating accounts payable to improving forecasting and fraud detection.
- Build AI Literacy. Help finance teams see AI as an augmentation tool, not a threat. Invest in upskilling while identifying gaps – from data management to AI model oversight.
- Set AI Governance Frameworks. Define accountability, roles, and control mechanisms to ensure responsible AI use across finance.
- Stay Ahead of the Curve. Monitor emerging tech that can streamline finance and bring in expert partners to fast-track AI adoption and results.
CFOs: From Gatekeepers to Growth Drivers
AI is not just a tech shift – it’s a CFO mandate. To lead, CFOs must embrace three roles: Investor, ensuring every AI bet delivers real ROI; Risk Guardian, protecting data integrity and compliance in a world of new risks; and AI Champion, embedding AI into finance teams to boost speed, accuracy, and insight.
This is how finance moves from record-keeping to value creation. With focused leadership and smart collaboration, CFOs can turn AI from buzzword to business impact.

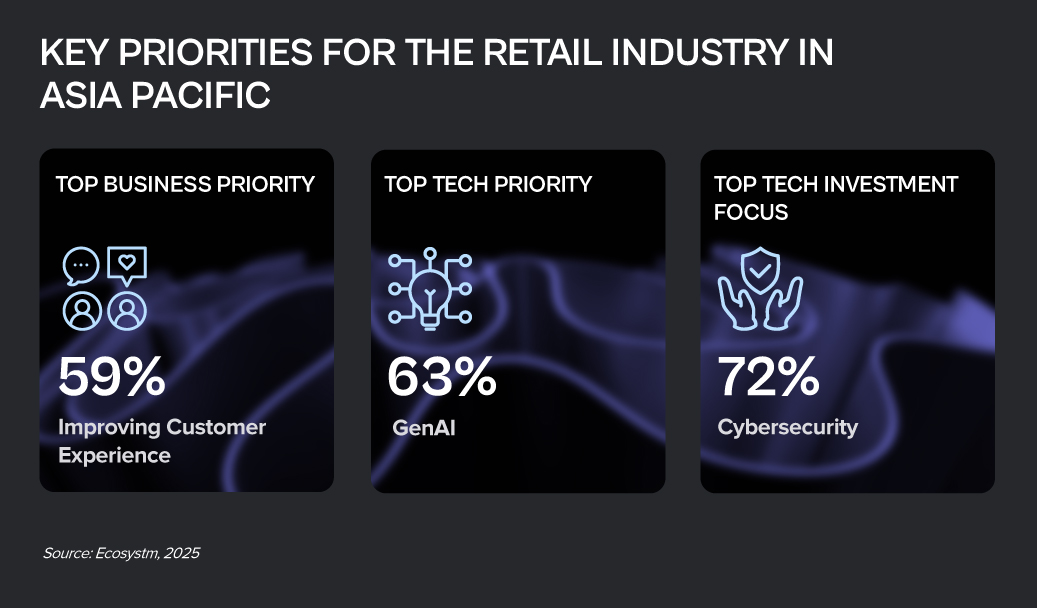
Retail transformation is a continuous, dynamic journey of reinvention – driven by agility, experimentation, and the need to keep pace with ever-evolving consumer behaviour. It’s not a fixed destination but an ongoing process of innovation.
At its heart, retail transformation is about putting the customer squarely in control. It’s the strategic overhaul that allows retailers to truly understand individual desires, offering hyper-personalised journeys that blur the lines between online browsing and in-store discovery.
Click here to download “Future Forward: Reimagining Retail” as a PDF.
Enabling Growth with Smarter Sales and Distribution
India’s Tata Consumer Products, aiming to grow their FMCG market share, set out to digitise sales across the vast ‘kirana’-driven retail network.
The company replaced outdated tools with a system that streamlines distributor onboarding, order management, and retail execution – cutting setup times from days to minutes.
A mobile app gives field reps real-time inventory, auto-applied promos, and personalised KPIs, while dashboards give managers live territory insights. Built in seven months, the platform now handles 6M+ transactions monthly, supports 8,000 reps, 12,000 distributors, and 1.6M outlets. Centralised service and rapid feature rollouts keep Tata Consumer fast, responsive, and customer-focused.
Addressing Legacy Limitations
One of New Zealand’s leading grocery retailer, Foodstuffs South Island, faced growing limitations from aging ERP systems and hardware nearing end-of-life.
Instead of reinvesting in outdated tech, FSSI launched Project Petra – a leap to a unified, cloud-based ERP platform.
The shift enabled intelligent replenishment, robotic automation, and a vastly improved user experience. In 18 months, FSSI streamlined roles, rebuilt core apps, and completed a smooth go-live in just three days. The payoff: forecasting and replenishment times cut by up to 50%, faster transactions, seamless price updates, and real-time insights. What began as a tech upgrade became a full transformation – boosting agility, empowering teams, and fuelling future-ready growth.
Streamlining Workflows, Empowering Employees
UCC Group, the Japanese coffee pioneer, is brewing a transformation internally. With 88 locations across 21 countries, UCC faced mounting inefficiencies from outdated legacy systems – slow, complex workflows and clunky portals that frustrated employees and slowed approvals.
UCC replaced their legacy systems with a cloud-first, mobile-first platform.
VPNs were eliminated. Approvals that once took multiple logins now take one tap. A clean, co-designed portal replaced the old interface, putting ease of use first. E-signatures and digitised requests cut paper use by 90% – over 1.5 million forms saved. A new life-event portal launched in just one month, proving speed and simplicity can coexist. Now expanding globally, UCC is unifying ERP, data, and apps into a single, employee-first hub – built for scale, speed, and the future.
Scaling Customer Experience at Speed
Aditya Birla Fashion Retail Limited (ABFRL) faced the challenge of scaling their multi-brand presence without compromising customer experience. As growth surged across stores, online platforms, and marketplaces, their order management system struggled to keep up – putting fulfillment speed, accuracy, and satisfaction at risk.
To solve this, ABFRL implemented a scalable, multi-instance order management solution that streamlined inventory tracking, fulfillment, and refunds.
The result: 99.5% faster inventory sync, zero refund failures, smarter order decisions, and accurate delivery estimates across all channels. This strategic overhaul helped ABFRL maintain service excellence while fuelling sustainable growth – proving that operational agility is key to scaling customer experience at speed.
Solving Reliability & Scalability Challenges
Chicks Lifestyle is a trusted home-grown brand in Hong Kong known for quality innerwear and thermal wear. As they expanded online and geared up for sustainable growth, outdated on-prem systems began to strain under peak-season pressure – causing crashes, long checkout lines, and customer frustration.
To fix this, they migrated their core ERP and POS systems to the cloud in just six weeks with zero data loss.
The result: 99.99% uptime, 30% jump in efficiency, 15% faster checkouts, and 40% lower IT costs. Loyalty data access dropped from minutes to seconds, enabling personalised service at scale. With a stable, scalable tech backbone in place, Chicks Lifestyle is now exploring AI to power their next phase of innovation.

What if your bank could predict your financial needs before you even realised them? Imagine a financial institution that understands your behaviours, anticipates your needs, and engages with you meaningfully in real time. That’s the power of modern marketing. We’re not talking about one-size-fits-all campaigns; we’re talking about creating personalised experiences that resonate on an individual level. Financial institutions are increasingly recognising that when marketing is done right, it becomes a powerful driver of customer loyalty and growth.
Take Netflix, for example – the frontrunner in personalisation. They don’t just serve content; they study audience preferences to deliver exactly what each viewer wants. Now, picture banks doing the same. Banks can apply the same principles by building a complete view of each customer based on transactions, preferences, and lifestyle signals. This allows them to deliver personalised content, products, and nudges that help customers make smarter financial decisions – and feel more understood in the process.
The Opportunity: Marketing Beyond the Surface
The real opportunity for banks today is to reimagine marketing – not as a support function, but as a strategic growth engine. This means pulling marketing out of the back office and placing it at the heart of business decision-making. When marketing is deeply embedded in strategy, aligned with business goals, and backed by executive support, it becomes a force multiplier. Cross-functional teams start working in sync, campaigns become smarter and more personalised, and outcomes become measurable and meaningful. The impact? Rapid customer growth, stronger retention, and sharper product uptake. This reimagination hinges on two foundational shifts:
- Culture Shift. Agile, cross-functional teams that focus on delivering specific customer outcomes rather than managing marketing channels in silos. These teams are empowered to act quickly, experiment, and refine based on feedback.
- Tech-Enabled Precision. A well-governed MarTech stack that enables real-time personalisation by effectively using data, decisioning models, and delivery mechanisms. This means moving from siloed systems to unified, intelligent platforms.
When these shifts align, marketing transforms from a function into a growth engine – fuelling innovation and building deeper customer relationships.
Embracing Modern Marketing Principles
Modern marketing starts with a few foundational shifts.
1. Embedding Marketing into Business Strategy. Marketing needs to be part of business strategy from the start – not bolted on at the end. When marketers have a seat at the table during strategy planning, they can shape priorities, align efforts, and measure impact more effectively.
This requires:
- Early involvement in strategic decision-making
- Marketing scorecards derived from business KPIs
- A unified voice across product, marketing, and operations
Also, Internal teams must be in sync with customer promises made externally. This means training, communication, and shared understanding across departments to ensure every touchpoint reinforces a consistent message. Whether it’s a branch interaction, a call centre response, or a chatbot exchange – each moment becomes a reflection of the brand’s commitment.
By embedding marketing within the business from the outset and aligning it with internal delivery mechanisms, organisations are better positioned to deliver on their promises and build lasting trust.
2. Turning Data into Action: Using MarTech for Smarter Decisions and Delivery. Modern marketing runs on data – but it only matters if it drives action. Banks need a systematic approach to turning raw data into relevant, timely customer experiences.
- Organise. Cleanse and consolidate data to form a single view of each customer.
- Decide. Apply AI/ML models to extract insights, make predictions, and personalise offerings.
- Deliver. Communicate through the most effective channels at the right moment.
But a smart stack needs structure. MarTech governance is essential to ensure tech investments are strategic – not duplicative. A cross-functional steering committee, with voices from marketing, IT, compliance, and business leadership, should guide decisions. This keeps tools aligned with business goals and ensures interoperability.
Equally important is fostering a culture of experimentation. A/B testing and continuous learning should be baked into campaign design – not as add-ons, but as core capabilities. This sharpens performance and fuels innovation by quickly scaling what works. Each test becomes a feedback loop, feeding a smarter, more agile marketing engine.
Embedding these practices into the data-decisioning-delivery loop helps banks move from scattered insights to coordinated, high-impact engagement.
3. Outcome-Focused Teams and Operating Models. Rather than being structured around traditional channels, high-performing marketing teams operate around customer journeys and outcomes. Agile squads can be created for:
- Seamless onboarding
- Product activation and adoption
- Retention and cross-sell strategies
These squads have to be multidisciplinary – combining marketing, data science, engineering, and product. They need to be empowered to experiment, move fast, and own KPIs tied to customer impact.
Outcome-driven teams focus on delivering measurable value – not just activity. For instance, a squad working on onboarding might track completion rates and activation time, while a cross-sell squad may target conversion on tailored offers. The shift to outcome-oriented delivery ensures that efforts are tied to clear business metrics, with faster feedback loops and accountability.
By storing, organising, and analysing customer data, banks equip these teams to predict needs more accurately. Insights fuel smarter decisions – enabling real-time, context-aware offers. Paired with agile delivery, this data-led approach makes every interaction timely, relevant, and impactful.
This approach ensures agility, accountability, and focus. By reducing reliance on rigid departmental structures, teams can iterate quickly and deliver greater value across the customer lifecycle.
The Modern Marketing Imperative
As customer needs and expectations evolve, marketing must adapt to modern standards, with a tighter alignment between business and marketing to deliver delightful customer experiences and impactful outcomes. These are the new imperatives for growth.
These principles are not just theoretical – they’re actionable steps that enable banks to anticipate needs, deliver hyper-personalised experiences, and build lasting relationships. By embracing this shift, banks can move from reactive to proactive, empowering customers to make smarter financial decisions while driving loyalty and growth. Ultimately, the future of banking lies in a personalised, integrated, and data-driven experience for every customer.

Customer Success leaders are keenly aware of AI’s burgeoning potential, and our latest research confirms it. AI is no longer a futuristic concept; it’s a present-day reality, already shaping content strategies for 55% of organisations and poised to expand its influence across a multitude of use cases.
Over the past two years, Ecosystm’s research – including surveys and deep dives with business and tech leaders – has consistently pointed to AI as the dominant theme.
Here are some insights for Customer Success Leaders from our research.
Click here to download “AI Stakeholders: The Customer Success Perspective” as a PDF.
AI in Action: Real-World Applications
The data speaks for itself. We’re seeing a significant uptake of AI in automating sales processes (69%), location-based marketing (63%), and delivering personalised product/service recommendations (61%). But beyond the numbers, what does this look like in practice?
In Marketing, AI tailors campaigns in real time based on customer behaviour, ensuring content and offers resonate. For e.g. in the Travel industry, AI analyses customer preferences to create customised itineraries, boosting satisfaction and repeat bookings. In Sales, AI-driven analysis of buying patterns helps teams stay ahead of trends, equipping them with the right products to meet demand. In Customer Experience, AI-powered feedback analysis identifies pain points before they escalate, leading to proactive problem-solving. We have already seen organisations using conversational AI to enable 24/7 customer engagement, instantly resolving issues while reducing team workload and enhancing CX.
Challenges and Opportunities: Navigating the AI Landscape
However, the path to AI adoption isn’t without its hurdles. Customer Success leaders face significant challenges, including the lack of an organisation-wide AI strategy, data complexity and access issues, and the cost of implementation.
Despite these challenges, the focus on AI to enhance Customer Success is evident, with nearly 40% of AI initiatives geared towards this goal. This requires a more active role for these leaders in shaping AI strategies and roadmaps.
Our research reveals that there lies a critical gap: Customer Success leaders have limited involvement in AI initiatives. Only 19% are involved in identifying and prioritising use cases, and a mere 10% have input into data ownership and governance. This lack of participation is a missed opportunity.
The 2025 Vision: AI-Driven Customer Success
Looking ahead, Customer Success leaders expect AI to deliver significant benefits, including improved customer experience (56%), increased productivity (50%), and enhanced innovation (44%). These expectations underscore AI’s pivotal role in shaping the future of customer success.
To fully harness AI’s potential and advancements like Agentic AI, leaders must take a more active role. This means driving a clear AI strategy, tackling data challenges, and working closely with IT and data science teams to ensure AI solutions address real customer pain points and business gaps.

The Asia Pacific region is rapidly emerging as a global economic powerhouse, with AI playing a key role in driving this growth. The AI market in the region is projected to reach USD 244B by 2025, and organisations must adapt and scale AI effectively to thrive. The question is no longer whether to adopt AI, but how to do so responsibly and effectively for long-term success.
The APAC AI Outlook 2025 highlights how Asia Pacific enterprises are moving beyond experimentation to maximise the impact of their AI investments.
Here are 5 key trends that will impact the AI landscape in 2025.
Click here to download “The Future of AI-Powered Business: 5 Trends to Watch” as a PDF.
1. Strategic AI Deployment
AI is no longer a buzzword, but Asia Pacific’s transformation engine. It’s reshaping industries and fuelling growth. Initially, high costs and complex ROI pushed leaders toward quick wins. Now, the game has changed. As AI adoption matures, the focus is shifting from short-term gains to long-term, innovation-driven strategies.
GenAI is is at the heart of this shift, moving beyond the periphery to power core business functions and deliver competitive advantage.
Organisations are rethinking AI investments, looking beyond pure financials to consider the impact on jobs, governance, and data readiness. The AI journey is about balancing ambition with practicality.

2. Optimising AI: Tailored Open-Source Models
Smaller, open-source, and specialised AI models will gain momentum as organisations seek efficiency, flexibility, and sustainability in their AI strategies.
Unlike LLMs, which require high computational power, smaller, task-specific models offer comparable performance while being more resource-efficient. This makes them ideal for organisations working with proprietary data or limited computational resources.
Beyond cost and performance, these models are more energy-efficient, addressing growing concerns about AI’s environmental impact.
3. Centralised Tools for Responsible Innovation
Navigating the increasingly complex AI landscape demands unified management and governance. Organisations will prioritise centralised frameworks to tame the chaos of diverse AI solutions, ensuring compliance (think EU AI Act) while boosting transparency and security.
Automated AI lifecycle management tools will streamline oversight, providing real-time tracking of model performance, usage, and issues like drift.
By using flexible developer toolkits and vendor-agnostic strategies, organisations can accelerate innovation while maintaining adaptability, as the technology evolves.
4. Supercharging Workflows With Agentic AI
Organisations will embrace Agentic AI to automate complex workflows and drive business value. Traditional automation tools struggle with real-world dynamism, but AI-powered agents offer a flexible solution. They empower autonomous task execution, intelligent decision-making, and adaptability to changing circumstances.
These agents, often using GenAI, understand complex instructions and learn from experience. They collaborate with humans, boosting efficiency, and adapt to disruptions, unlike rigid traditional automation.
Agentic workflows are key to redefining work, enabling agility and innovation.

5. From Productivity to People
The focus of AI conversations will shift from simply boosting productivity to using AI for human-centric innovation that transforms both employee roles and customer experiences.
For employees, AI will handle routine tasks, enabling them to focus on creativity and innovation. Education and training will be crucial for a smooth transition to AI-powered workflows.
For customers, AI is evolving to offer more empathetic, personalised interactions by understanding individual emotions, motivations, and preferences. Organisations are recognising the need for transparent, explainable AI to build trust, tailor solutions, and deepen engagement.
Hit or miss AI experiments have leaders demanding results. In this breakneck AI landscape, strategy and realism are your survival tools. A pragmatic approach? High-impact, achievable goals. Know your capabilities, prioritise manageable projects, and stay flexible. The AI winners will be those who champion human-AI collaboration, bake in ethics, and never stop researching.